Overview of Cloud Technologies
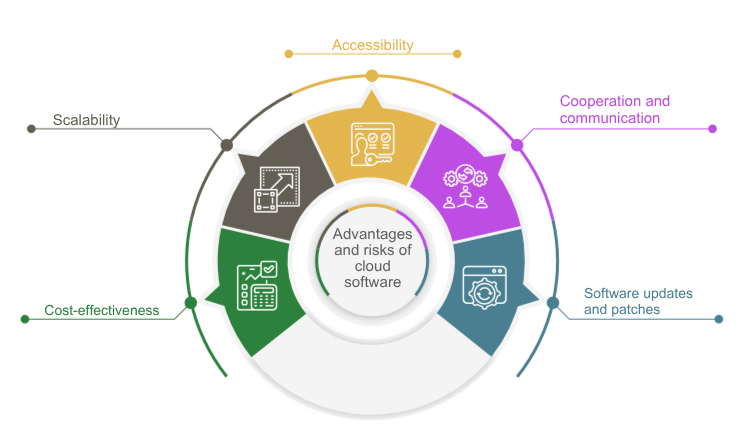
Cloud computing has evolved rapidly in recent years and has become a key technology across many industries. At its core, it involves delivering IT resources over the internet, enabling companies and organizations to access powerful servers, storage capacity, and applications without having to invest in expensive hardware. This technology offers numerous advantages, including scalability, flexibility, cost efficiency, and the ability to access data and applications from anywhere in the world.
Cloud technologies are now used in a wide range of areas, from data processing and storage to software development, artificial intelligence, and machine learning. Organizations use cloud services to optimize business processes, shorten innovation cycles, and remain competitive. The public sector is also increasingly adopting cloud solutions, especially social service organizations.
Importance for Social Service Organizations
For social service organizations, which often operate with limited financial means and, in many cases, limited staffing resources, cloud solutions offer significant benefits. By using cloud computing, these organizations can modernize their IT infrastructure without making major upfront investments. The flexibility and scalability of the cloud allow social organizations to adjust their resources based on actual needs, helping them work more efficiently and effectively.
Cloud solutions also improve collaboration and communication. Cloud-based platforms enable social service organizations to exchange information seamlessly and work together in real time, regardless of geographic location. This is particularly important at a time when digital transformation and remote work are becoming increasingly significant.
Implementing cloud technologies also helps social service organizations store and manage their data securely. Cloud providers invest heavily in security measures and can often offer stronger protection against data loss and cyberattacks than many traditional on-premises IT solutions.
Overall, the use of cloud solutions opens up new opportunities for social service organizations to improve their services while increasing operational efficiency.
Benefits and Risks of Cloud Software
Benefits
Risks

Data Protection and Data Security
Data Protection Laws
In Europe, the General Data Protection Regulation (GDPR) governs the handling of personal data. The GDPR sets strict requirements for the processing and protection of this data. Key aspects include the consent of the data subjects, the right to access and erasure, data minimization, and the obligation to report data breaches within 72 hours.
In addition to the GDPR, various countries have supplementary data protection laws that must also be observed. In Germany, for example, the Federal Data Protection Act (BDSG) complements the requirements of the GDPR. These laws are intended to protect people’s privacy and ensure that their data is processed responsibly and securely.
Specific Requirements for Social Service Organizations
Social service organizations are subject to particular requirements when implementing data protection laws. Because these organizations often work with especially sensitive data such as health information, social data, or data relating to vulnerable individuals, a very high level of protection is required. Social service organizations must ensure that only authorized persons have access to this data and that it is protected against unauthorized access, loss, or misuse.
Transparency is another key element. Social service organizations must inform individuals about which data is being collected, why it is needed, and how it is processed. This also includes the obligation to grant access to personal data upon request and to delete it if requested, provided that no statutory retention requirements apply.
Security Measures
Encryption
Encrypting data is a fundamental element of data security. It protects both stored and transmitted data from unauthorized access. By implementing encryption technologies, social service organizations can ensure that sensitive information remains protected even if it falls into the wrong hands.
There are two main types of data encryption: encryption of stored data (data at rest) and encryption of transmitted data (data in transit). Data at rest should be encrypted on hard drives, in databases, and on other storage media. Data in transit should be encrypted using secure protocols such as HTTPS or TLS to protect it from interception and tampering during transmission.
Cloud data is encrypted both during transmission (in transit) and while stored (at rest). This protects data against unauthorized access and ensures that even in the event of a data breach, the information remains unreadable.
Access Controls
Cloud providers implement strict access control mechanisms to ensure that only authorized individuals can access the data. This includes the use of two-factor authentication (2FA), role-based access control (RBAC), and regular reviews of access rights.
Firewalls and Intrusion Detection Systems (IDS)
Firewalls protect cloud infrastructure from unauthorized access and malicious traffic. Intrusion Detection Systems monitor network activity and identify unusual patterns that may indicate a security incident.
Security Certifications and Standards
Many cloud providers are certified according to international security standards such as ISO/IEC 27001, SOC 2, and GDPR compliance frameworks. These standards define strict requirements for data protection and data security.
DDoS Protection
Protection against Distributed Denial of Service (DDoS) attacks is an essential part of cloud software security. DDoS attacks aim to disable a service by overwhelming it with a flood of requests, which can overload resources and ultimately cause service outages. Automated systems analyze traffic and identify potentially harmful activity in order to initiate immediate countermeasures. By limiting the number of requests per unit of time from a specific source (rate limiting) and controlling data flow (throttling), the impact of DDoS attacks can be minimized. These measures help maintain legitimate traffic while blocking malicious requests.
User Responsibility
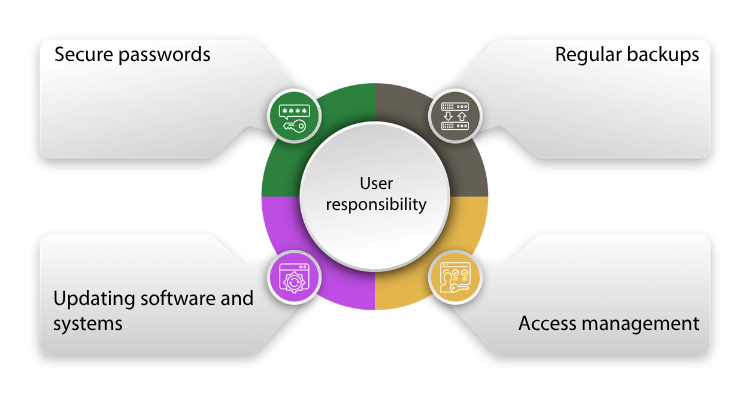
In addition to the security measures implemented by cloud providers, social service organizations must also actively contribute to data security themselves.
Key measures include:
Employee Awareness
Training and raising employee awareness about data protection and data security are crucial to protecting data in social service organizations.

Here are some measures that should be taken:
Conclusion
The use of cloud solutions in social service organizations offers numerous advantages that go far beyond simple IT cost savings. By using cloud computing, social organizations can modernize their IT infrastructure and flexibly adapt it to their needs without having to make major investments. Increased scalability, accessibility, and improved collaboration and communication through cloud-based tools all make a substantial contribution to enhancing the efficiency and effectiveness of social services.
Despite the many benefits, there are also challenges and risks that must be considered. A reliable internet connection is essential, and concerns regarding data security and privacy must be taken seriously. It is crucial that both cloud providers and social service organizations themselves implement comprehensive security measures and update them regularly. This includes encrypting data, enforcing strict access controls, and training employees in the secure handling of sensitive information.
The future of cloud technologies in social service organizations promises further progress and innovation, enabling these organizations to fulfill their mission even more effectively. By strategically combining technological progress with organizational measures, social service organizations can gain the greatest possible benefit from cloud solutions while maintaining a high standard of data protection and data security.