Many companies now have an ISMS, or Information Security Management System. In principle, this means a structured, holistic approach to planning, implementing, monitoring, and continuously improving information security. In practice, however, the picture is often different: risk registers are maintained in Excel, actions are documented in Word, and evidence is collected only shortly before an audit.
This is exactly where the problem lies. The threat landscape does not operate in audit cycles. Companies around the world are facing a growing number of cyberattacks, sabotage attempts, supply chain risks, and identity-based attacks. Phishing, ransomware, account takeovers, and compromised third parties have long since become part of the day-to-day reality for many security teams. At the same time, the cost of individual security incidents continues to rise, whether through operational disruption, recovery efforts, reputational damage, or regulatory consequences.
Against this backdrop, an ISMS maintained primarily for certification purposes is no longer enough. This is not only a practical issue, but also a conceptual one. ISO/IEC 27001 is explicitly designed for the “establishing, implementing, maintaining and continually improving” of an ISMS. In other words, the standard is not intended as a one-time documentation exercise, but as a system that is reviewed, managed, and improved on an ongoing basis.
Why a “Living” ISMS Will Become the Norm in 2026
Pressure is increasing from three directions at once: the threat landscape, regulatory requirements, and management expectations. Across the world, governments, regulators, and industry frameworks are tightening their requirements for cyber resilience, governance, and demonstrable compliance. Whether through sector-specific requirements, international standards, or regional frameworks such as DORA and NIS 2, the direction is clear. What is expected today is no longer just documented intent, but demonstrable effectiveness.
At the same time, attack dynamics are changing. Modern attacks are faster, more automated, and often multi-staged. AI-supported phishing campaigns, social engineering via collaboration platforms, identity abuse, and attacks through third parties are adding further complexity. Any organization that reassesses risks only once a year is reacting too slowly to this reality.
As a result, the benchmark for information security is changing as well. In 2026, the decisive factor is no longer an organization’s ability to document compliance with ISO 27001, but the ability of its ISMS to continuously and transparently reflect risks, controls, vulnerabilities, third-party risks, and compliance evidence.
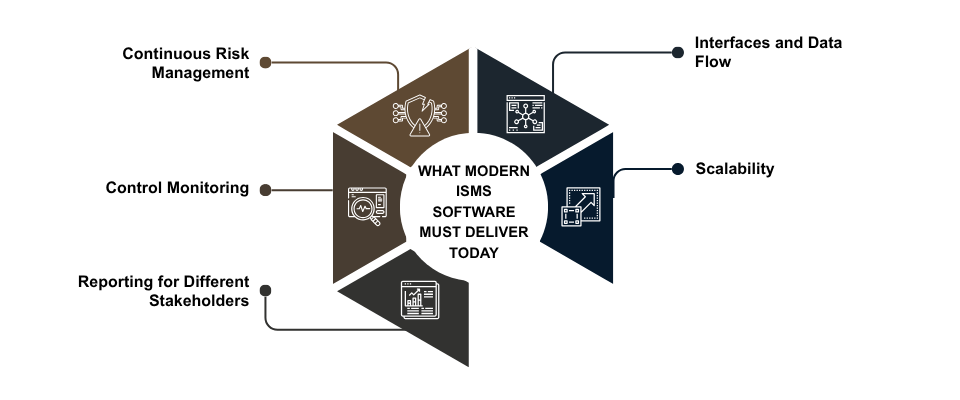
What Modern ISMS Software Must Deliver Today
What You Should Ask Vendors in 2026
For a structured software evaluation, it makes sense to use a question set that goes beyond general product presentations:
-
Does the software automatically trigger a risk reassessment when incidents, vulnerabilities, or changes occur?
-
Can risks, controls, actions, assets, and owners be linked directly to one another?
-
How is audit evidence collected, versioned, and stored in an audit-proof way?
-
Which standards and frameworks are supported natively, such as ISO/IEC 27001:2022, NIS 2, DORA, or other industry-specific requirements?
-
Does the solution provide a robust model for supplier and third-party risks?
-
Which dashboards are available for management, security leaders, and audit teams?
-
Which integrations exist for SIEM, ITSM, IAM, or vulnerability management?
-
How granular are roles, approvals, and permissions?
-
How much manual effort is required during day-to-day operation?
-
Which data can be exported or transferred into other systems?
In addition, a proof of concept using real-world use cases is highly advisable. Do not test only the user interface, but also typical everyday scenarios: a newly identified risk, missing audit evidence, or a supplier risk requiring escalation. This quickly shows whether the solution performs under real conditions.
Conclusion
In 2026, an ISMS is no longer just a certification project. It is a management system that must make risks, actions, and effectiveness continuously visible. That is entirely in line with the spirit of ISO 27001: not documenting once, but improving continuously.
At the same time, expectations around timeliness, transparency, demonstrable compliance, and governance are rising worldwide. That is why organizations selecting ISMS software today should not focus primarily on certification support, but on finding a tool for continuous security management.
The strategic difference is significant: a “paper ISO” becomes a system that actively manages information security and supports it effectively in everyday operations.
Compare ISMS software on SoftGuide.com now and filter specifically for solutions covering ISO 27001, audit evidence, risk management, and integrations.